Category Archives: Technology
-

Observing Android VPN Leaks with the pcWRT Router
Posted on January 24, 2025 by pcwrt in Security, Technology, VPN.It is known that Android leaks connectivity checks and DNS traffic outside a VPN tunnel under certain circumstances, even when the “Block connections without VPN” switch is turned on. These problems remain unfixed today basically because Google thinks these are not problems. I quote part of the response from Google below: The connectivity checks are […]
Continue Reading... No Comments. -
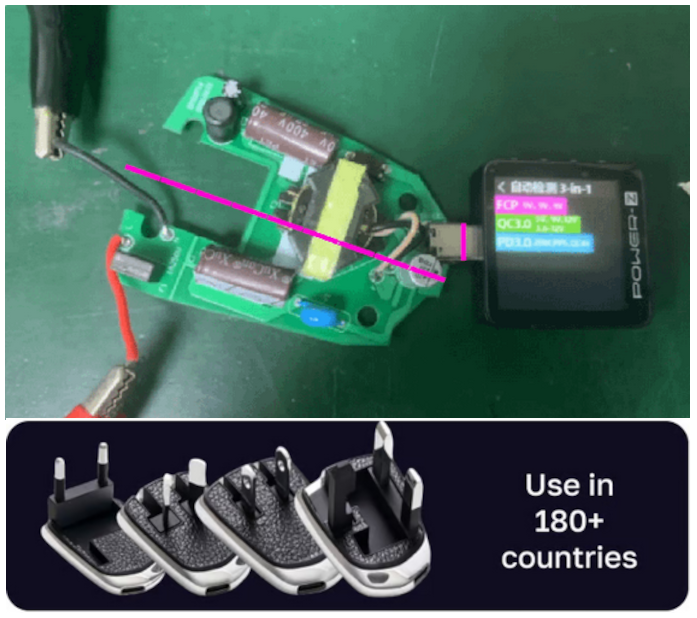
Is the MELLO charger a scam (Kickstarter)?
Posted on June 3, 2024 by pcwrt in News, Technology.Kickstarter is no stranger to scammers. Projects surpassed their goals spectacularly and yet fail to deliver. Did the projects fail despite of honest efforts or were there no intention to fulfill the promises on the outset? It’s hard to tell. WeTag made extravagant claims for their iTag battery free item locating tag without a prototype […]
Continue Reading... No Comments. -
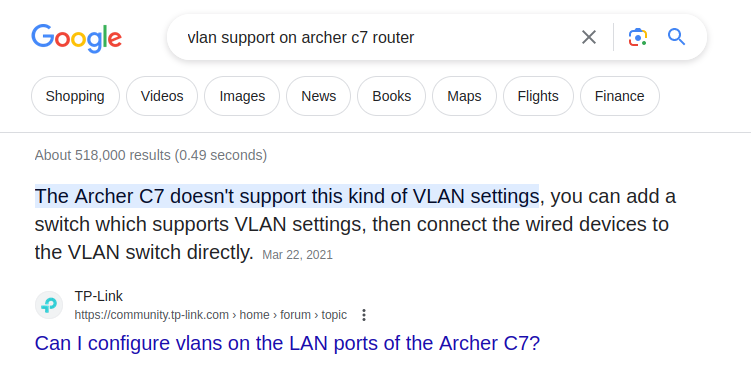
Using ChatGPT and Bard to Find a Tech Product
Posted on May 16, 2023 by pcwrt in Technology.The pcWRT router provides some unique features which are not common among consumer grade products. One such feature is VLAN support. Keyword searches usually don’t work well when a potential customer wants to find products supporting a specific technical feature. So we are trying to find out if AI technologies like ChatGPT and Google Bard […]
Continue Reading... No Comments. -
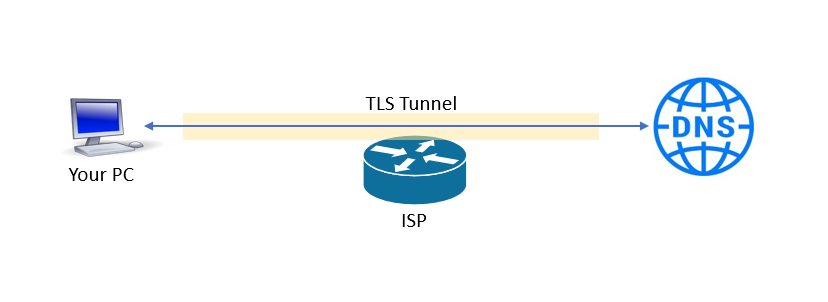
What is the best DNS for privacy?
Posted on December 1, 2021 by pcwrt in Security, Technology.With the default configuration, your router uses DNS servers run by your ISP. As such, the ISP can easily collect information about the websites you’re visiting (and the apps you’re using). You can override the router’s default settings to make it use other DNS services such as OpenDNS, Quad9 or Cloudflare. But since the DNS […]
Continue Reading... No Comments. -
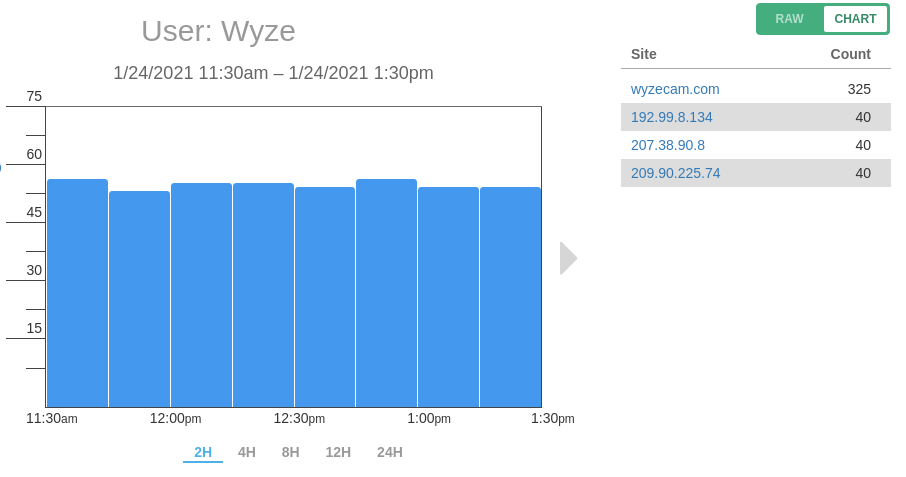
Is WyzeCam Sending Data to Servers Other Than AWS?
Posted on January 26, 2021 by pcwrt in Security, Technology.When the WyzeCam started selling a few years back, there was an alarming review on Amazon stating that it was sending data all over the world. The reviewer claimed seeing traffic heading to China, Japan and Germany, among other locations. The review on Amazon is probably no longer available. But the discussion on Reddit is […]
Continue Reading... No Comments. -

How does my browser know my real location when I’m on a VPN?
Posted on January 8, 2021 by pcwrt in Technology, WiFi.On a computer that doesn’t have GPS and cellular connection, how does your browser get your location? The obvious answer is it uses your IP address. But that is not true. You can do two simple tests to confirm this: Open https://browserleaks.com/geo. Click Allow Location Access when prompted. Check your location and Accuracy. More likely […]
Continue Reading... No Comments. -
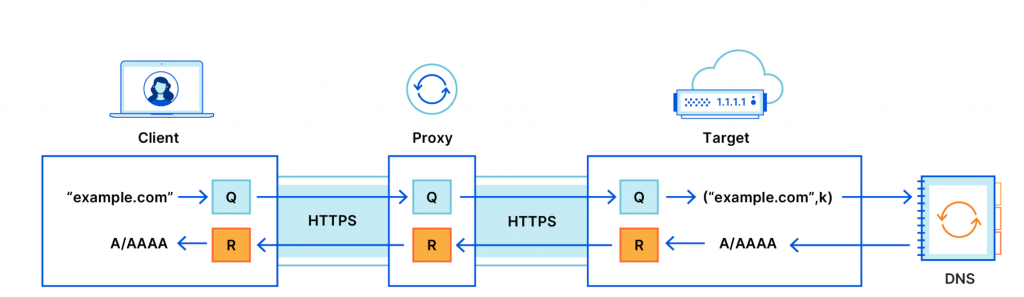
Oblivious DNS over HTTPS vs DoH through HTTP proxy
Posted on December 9, 2020 by pcwrt in Security, Technology.Cloudflare recently published a blog post on how Oblivious DNS over HTTPS (ODoH) works. According to the blog post, the purpose of ODoH is to separate the DNS queries from the originating IP addresses, preventing the DoH provider from seeing who’s sending the DNS requests. Thus improved privacy for clients. Schematically, this is how it […]
Continue Reading... No Comments. -

Does your parental control pass the DOH test?
Posted on October 7, 2020 by pcwrt in Parental Control, Technology.Why does DOH (DNS over HTTPS) interfere with parental control? Unlike traditional DNS queries, which are sent to servers via a plain text connection, DNS-over-HTTPS (DoH) requests are sent over an encrypted HTTPS connection. It was introduced mainly because of the privacy benefits that come with the data encryption. However, since many parental control systems […]
Continue Reading... 1 Comment. -

Netgear router vulnerability found (again), what can you do?
Posted on June 30, 2020 by pcwrt in News, Technology.Recently, researchers found an unpatched zero-day vulnerability in Netgear routers that potentially puts 79 device models at risk. According to the Zero Day Initiative: The specific flaw exists within the httpd service, which listens on TCP port 80 by default. The issue results from the lack of proper validation of the length of user-supplied data […]
Continue Reading... No Comments. -

Is it safe to enter credit card info on public WiFi?
Posted on May 11, 2020 by pcwrt in Security, Technology, WiFi.How big is the risk? Time and time again you’ve been told that public WiFi hotspots or compromised routers will get your credit card numbers and banking info stolen. However, such risks have been overly hyped. We agree that public, open WiFi networks totally cannot be trusted. And that compromised routers can be used to […]
Continue Reading... 1 Comment.