Category Archives: Security
-

Observing Android VPN Leaks with the pcWRT Router
Posted on January 24, 2025 by pcwrt in Security, Technology, VPN.It is known that Android leaks connectivity checks and DNS traffic outside a VPN tunnel under certain circumstances, even when the “Block connections without VPN” switch is turned on. These problems remain unfixed today basically because Google thinks these are not problems. I quote part of the response from Google below: The connectivity checks are […]
Continue Reading... No Comments. -
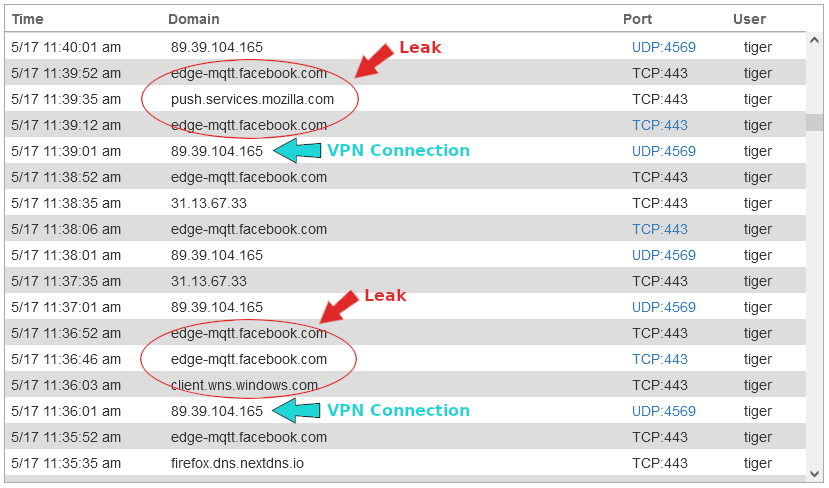
A VPN Leak in Windows 10
Posted on May 13, 2023 by pcwrt in Security, VPN.This is not your normal DNS or WebRTC leak. It is observed that preexisting network connections keep communicating outside the VPN tunnel long after the VPN connection is established. It looked like the iOS leak reported earlier, but this one is more of a VPN client problem than an OS level problem. The challenge with […]
Continue Reading... No Comments. -
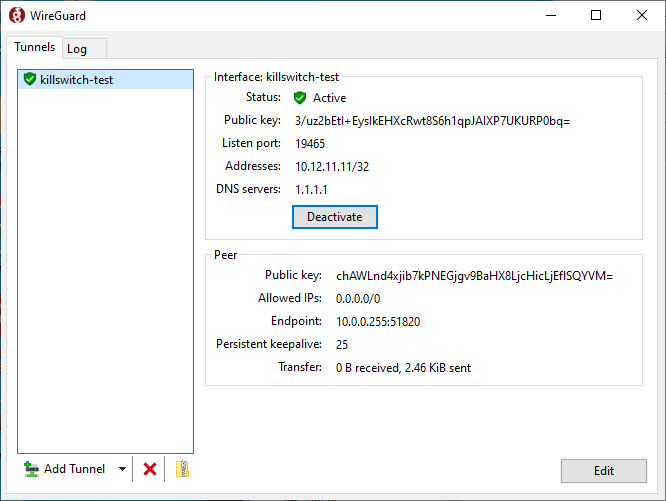
How to check that your VPN kill switch is working
Posted on June 15, 2022 by pcwrt in How To, Security, VPN.Many VPN apps come with a “kill switch”, which turns off your Internet connectivity when the VPN connection is lost. Without a kill switch, you might be falsely thinking that you’re protected by a VPN, while the VPN connection is down and your connection is switched back to the ISP. But how do you know […]
Continue Reading... 1 Comment. -
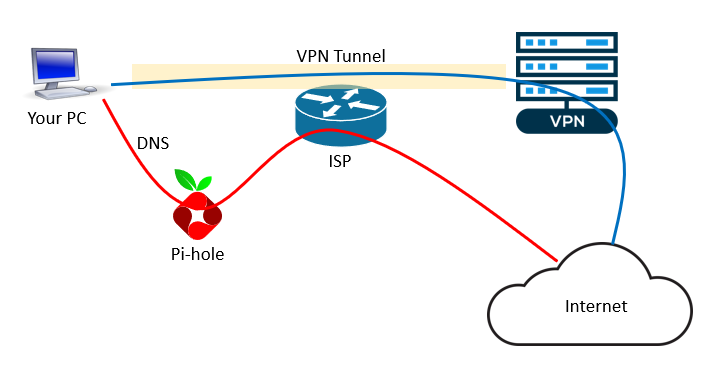
How to set up a VPN server at home (on the router)
Posted on December 16, 2021 by pcwrt in How To, Security, VPN.If you did some search on this topic, you are probably confused. Most articles on this topic confuse readers rather than helping them. Why you need a VPN server at home First of all, let’s make it clear that there’s only one reason to set up a VPN server at home: you want to access […]
Continue Reading... No Comments. -
What is the best DNS for privacy?
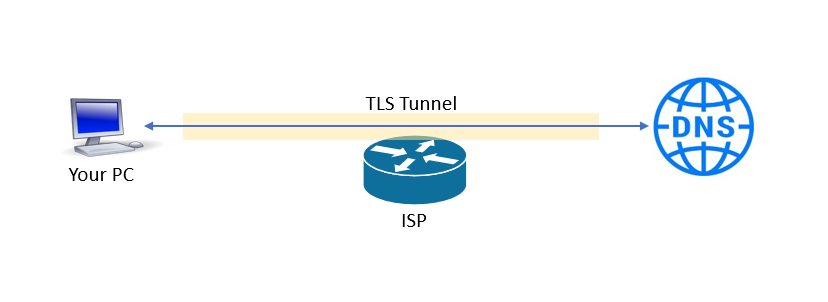
Posted on December 1, 2021 by pcwrt in Security, Technology.With the default configuration, your router uses DNS servers run by your ISP. As such, the ISP can easily collect information about the websites you’re visiting (and the apps you’re using). You can override the router’s default settings to make it use other DNS services such as OpenDNS, Quad9 or Cloudflare. But since the DNS […]
Continue Reading... No Comments. -
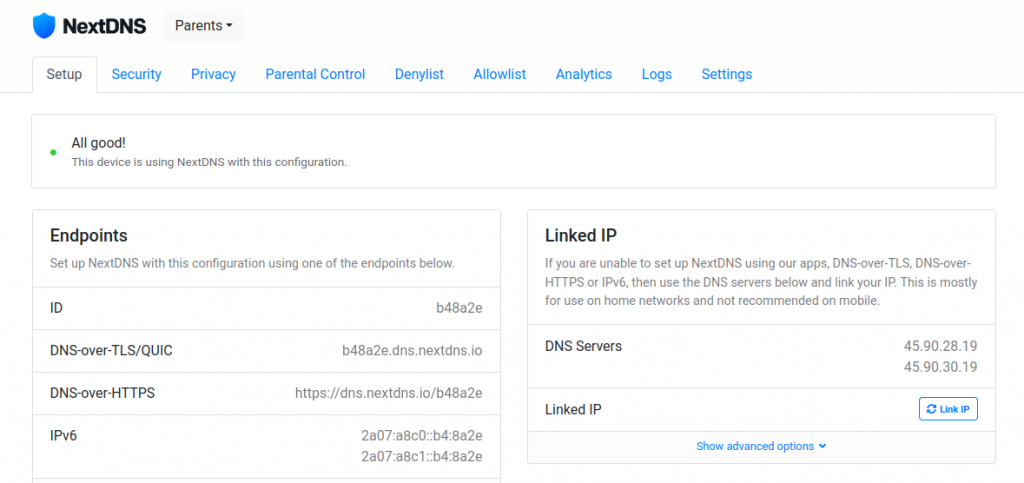
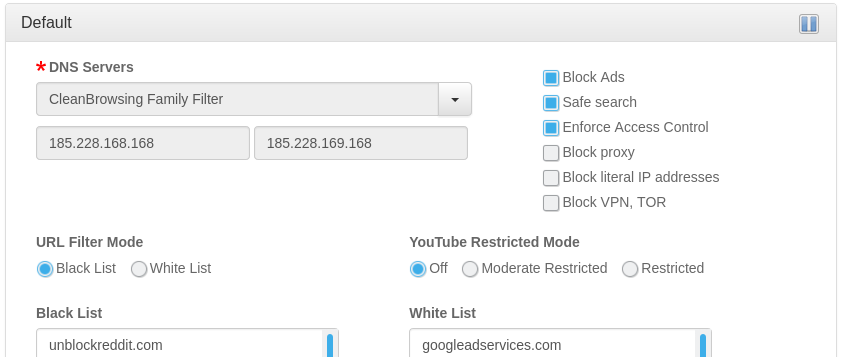
Set Up Multiple NextDNS Configurations for Encrypted DNS on the pcWRT Router
Posted on November 17, 2021 by pcwrt in How To, Router, Security.You can set up multiple configurations in NextDNS, each with different block lists. These configurations map neatly to the Access Control profiles on the pcWRT router. As a result, you can apply different NextDNS filtering configurations to different devices on your network directly from the router, without the need to set up NextDNS on each […]
Continue Reading... No Comments. -
6 VPN leak scenarios and how to prevent them
Posted on August 29, 2021 by pcwrt in Security, VPN.TL;DR: the pcWRT router naturally protects you from the 6 leak scenarios listed below (i.e., no extra work needed). But if you’re using another VPN solution, read on. 1. DNS Leak DNS Leak is the most common type of leak when you are connected to a VPN. Even after your VPN is successfully connected, there’s […]
Continue Reading... No Comments. -
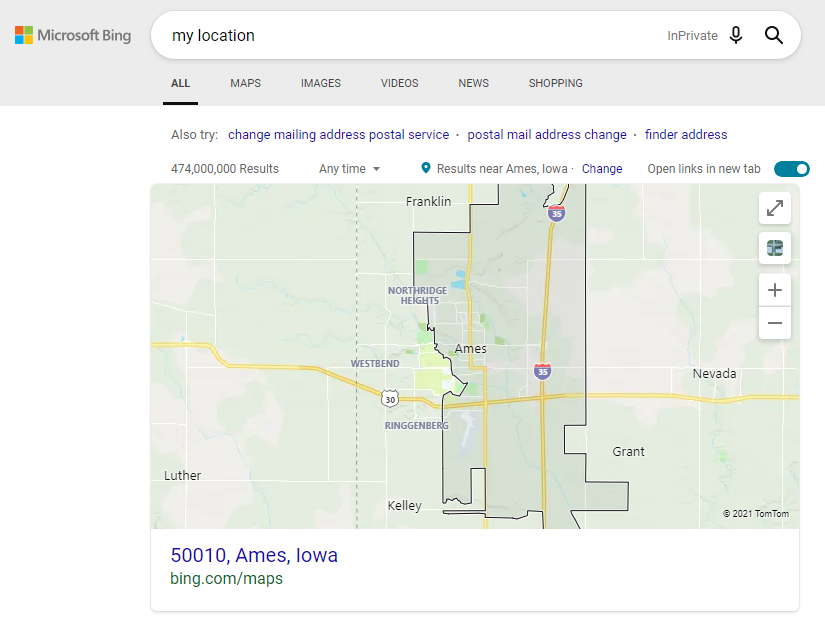
Is Google using fingerprinting to track you?
Posted on August 11, 2021 by pcwrt in Security, VPN.What’s your location? A post on Reddit reported that Google continues to display his actual address despite him using a VPN, turning off WiFi and blocking Geolocation. He even tried fresh installations. Intrigued by the post, I did the tests described here to understand the behavior. To eliminate the possibility of tracking by cookies, I […]
Continue Reading... No Comments. -
Use OpenDNS for Ad Blocking?
Posted on January 29, 2021 by pcwrt in Router, Security.A lot of people use OpenDNS on their home networks to block contents that might be harmful to children. Some were asking whether OpenDNS can add a filtering category to block unwanted ads. The answer from OpenDNS was no, and for good reason. As a result, if you want to use a DNS service to […]
Continue Reading... No Comments. -
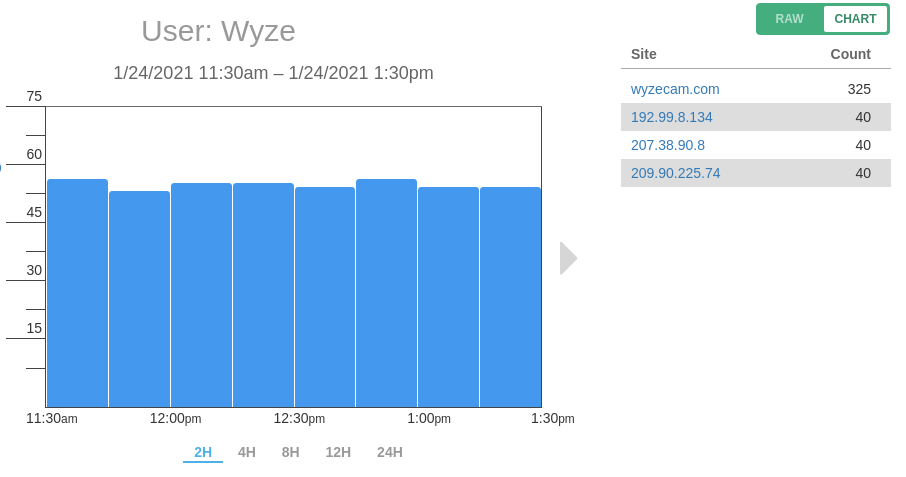
Is WyzeCam Sending Data to Servers Other Than AWS?
Posted on January 26, 2021 by pcwrt in Security, Technology.When the WyzeCam started selling a few years back, there was an alarming review on Amazon stating that it was sending data all over the world. The reviewer claimed seeing traffic heading to China, Japan and Germany, among other locations. The review on Amazon is probably no longer available. But the discussion on Reddit is […]
Continue Reading... No Comments.