-
What is the best DNS for privacy?
With the default configuration, your router uses DNS servers run by your ISP. As such, the ISP can easily collect information about the websites you’re visiting (and the apps you’re using). You can override the router’s default settings to make it use other DNS services such as OpenDNS, Quad9 or Cloudflare. But since the DNS queries pass through your ISP gateway and are not encrypted, your ISP can still collect your DNS info.
DoH/DoT alone is not enough
DNS encryption protocols, i.e., DNS over HTTPS (DoH) and DNS over TLS (DoT), encrypt your DNS queries before sending them over to the DNS service. Even though the queries still pass through your ISP gateway, the ISP can no longer see the domain names.
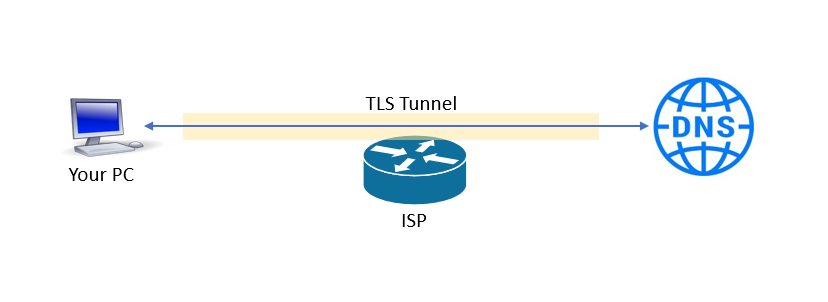
But now, the DNS service you’re using knows all your DNS queries and your IP address. Unless you’re really sure that the DNS service protects your privacy, you’re not in a much better position.
Add a VPN to the mix
When you establish a VPN connection to your VPN service, your DNS server switches to that of the VPN service. Therefore, your VPN provider knows all your Internet activities. Many (almost all?) VPN services promise no-logs policies, but some turned out not true. How do you hide your DNS queries from your VPN service?
As it turned out, you can get complete DNS privacy by tunneling DoH/DoT through a VPN.
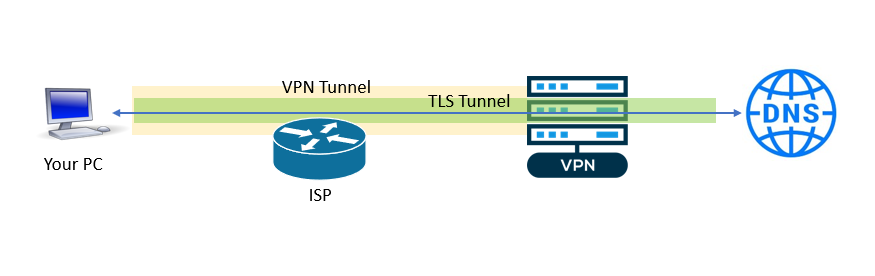
As can be seen from the picture above:
- The ISP cannot see what’s happening because the traffic is encapsulated in the VPN tunnel.
- The VPN service cannot see the DNS lookups because the queries are encrypted with TLS.
- The DNS service knows the domain names you’re looking up, but it doesn’t see your IP address.
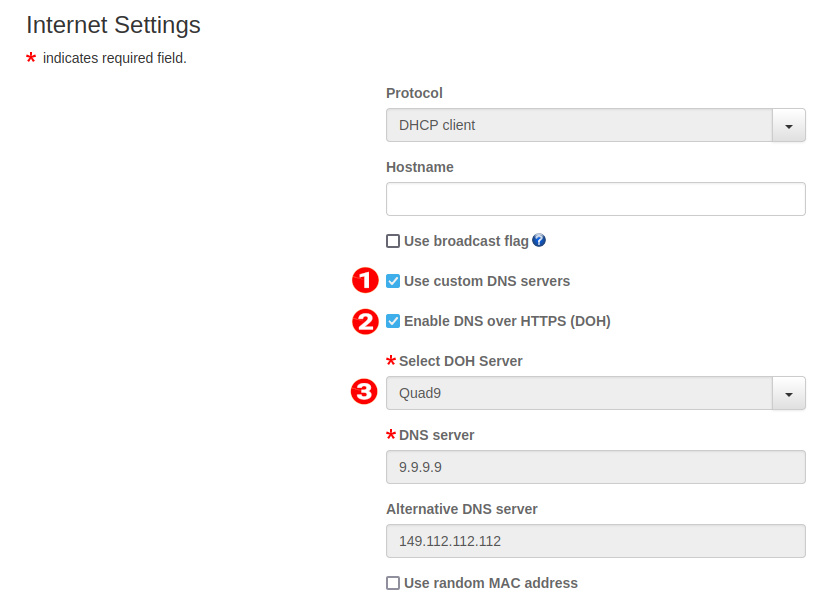
How to do this on the pcWRT router
On the pcWRT router, you can enable DNS over HTTPS (DoH) on the Internet Settings page. Once DoH is enabled on the router, the selected DoH service will be used for all your VPN client connections on the router, instead of the DNS service assigned by your VPN.
Here are the steps:
- Check “Use custom DNS servers”
- Check “Enable DNS over HTTPS (DOH)”
- Select the DOH server to use