-
Netgear router vulnerability found (again), what can you do?

Recently, researchers found an unpatched zero-day vulnerability in Netgear routers that potentially puts 79 device models at risk.According to the Zero Day Initiative:
The specific flaw exists within the httpd service, which listens on TCP port 80 by default. The issue results from the lack of proper validation of the length of user-supplied data prior to copying it to a fixed-length, stack-based buffer. An attacker can leverage this vulnerability to execute code in the context of root.
In essence, this vulnerability enables an attacker to take control of your router without knowing the router password.
Worse yet, since the vulnerability occurs before the Cross-Site Request Forgery (CSRF) token is checked, an attacker can break into your router when you browse a web page that contains malicious content..
News, but nothing new
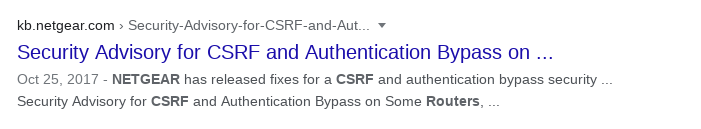
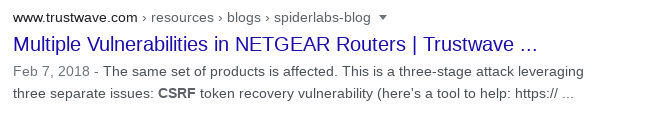
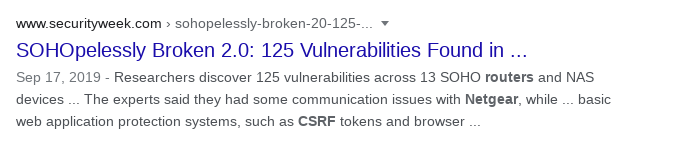
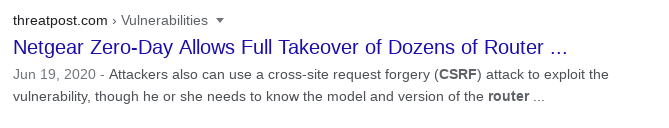
While this story may sound new, it is actually a repeating story. Enter “netgear router csrf” into Google, I found similar stories year after year.
What can you do?
Here are several things you can do:
- Update your router firmware when the patch is released
- Buy a new router
- Flash your router with open source firmware, such as OpenWrt or DD-WRT
- Buy a router built with open source firmware, such as pcWRT
The caveat with option 1 is, for some devices in the vulnerable list, Netgear no longer releases updates. Even if you get an update or get a new router, are you sure the same type of vulnerabilities won’t come back to bite you next year?
In our opinion, switching to open source firmware is the only viable option in the long run. Open source projects usually release security updates faster, and they support legacy hardware longer.
What can you do if none of the above is an option?
At the very least, you should try to stop CSRF. To do it properly, you need three steps:
- If you are using the default router password, change it. Choose a strong password. People have different opinions about what “strong” means, but you can’t go wrong with “long”.
- Change your router’s IP address. The hacker needs to know your router’s IP address in order to carry out a CSRF attack. Avoid common router IP addresses such as 192.168.0.1, 192.168.1.1, etc. Something like 172.25.152.1 with netmask 255.255.255.0 would make it harder for a hacker to guess. But make sure you pick an ip address from the private IP address range.
- Disable WebRTC in all your browsers. WebRTC leaks your internal IP address, which defeats the purpose of step 2 above. Just Duck how to disable WebRTC to find out how.
Warning: do not install browser extensions to disable WebRTC. It is not necessary and it may bring additional security risks.